NEW YORK – Deep inside a fortified, 41-story building in lower Manhattan, some of the FBI’s top agents and technical experts are trying to keep pace with one of the newest threats to the United States – cyber attacks.
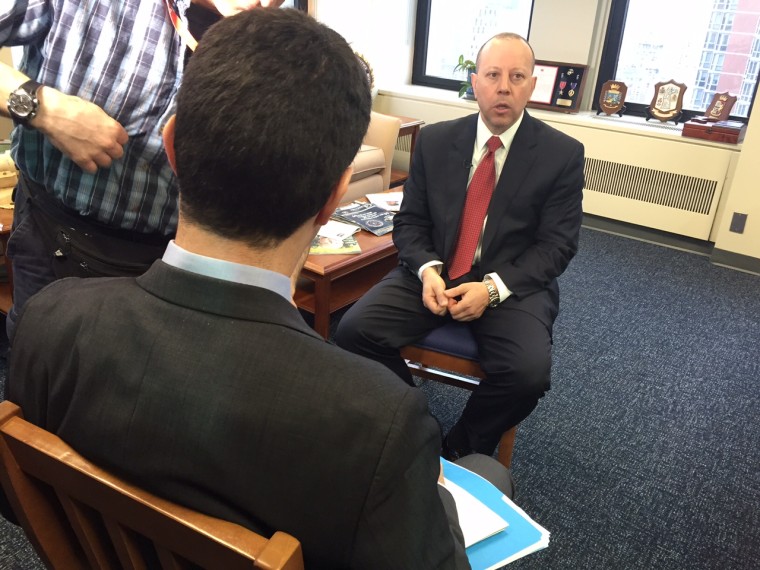
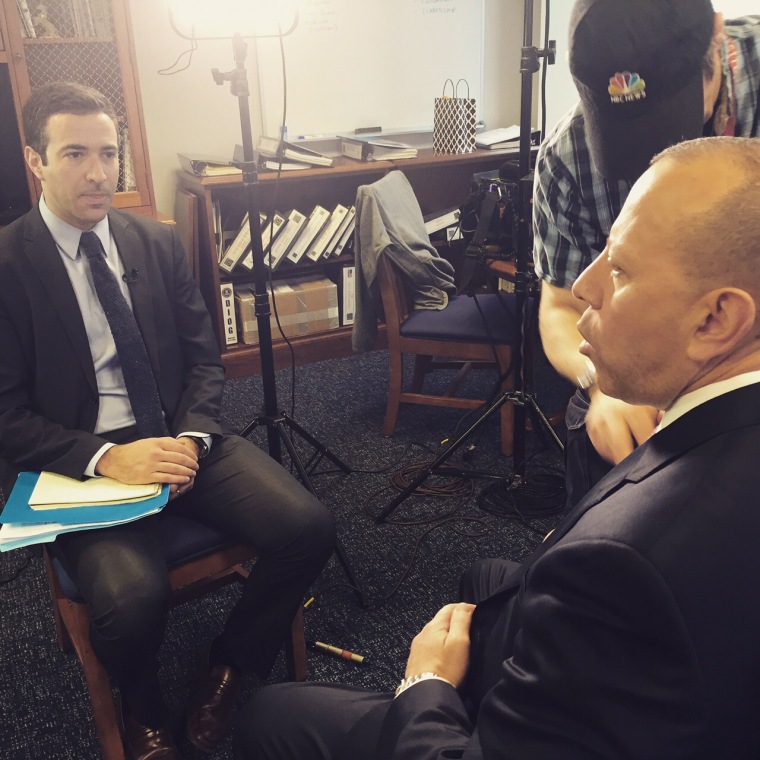
“The odds are, unfortunately, in favor of the hacker at this point,” says Leo Taddeo, special agent in charge of cyber and special operations here. “We're trying to change that.”
Taddeo, who began his career on the Gambino Family Organized Crime Squad and later led New York’s Counterterrorism Division, is combining traditional crime-fighting tactics with newer methods to counter virtual crime.
New York is a major target for both conventional terrorism and financial cyber crime, and while high-profile attacks like the Sony hack draw lots of attention, the mounting cyber threat to American business is often underestimated.
Cyber attacks on large companies are up by roughly 40%, according to a Symantec study released this week. Other surveys suggest most American corporations don’t even know when they’ve been hacked. “Sometimes it's the government that detects the breach, sometimes it's someone you're connected to that detects the breach,” Taddeo tells msnbc, “but in 70% of the cases, the breach is not detected by the victim.”
Investigators say breaches can go undetected for months at a time, which means hackers and foreign criminals may spend months compromising a company’s network without detection.
The FBI is recruiting computer experts and building out its cyber forensics department, including a national Computer Analysis Response Team, CART, which wades through a massive amount of data.
At the New York field office, technical specialists work out of a room packed with computers and data storage units, sorting through material seized from computers and phones for a range of open investigations.
A huge job
Cyber cases involve information on a scale far beyond any other crime. In the New York field office alone, over 80 terabytes of data are being processed – that amounts to over 200 warehouses of printed material, or eight times the text in the Library of Congress. Nationwide, the FBI says CART examined 10,000 terabytes of data in a single year.
It’s a huge job, and the bureau wants help. “We need cyber talent -- we want to encourage individuals who have a knack for cyber work meaning they're either effective hackers themselves,” Taddeo says, “or they're programmers or they're forensic experts.” While the bureau can’t compete with Silicon Valley on salary, agents believe they have something else to offer. The job combines projects which “can't be found in the private sector,” Taddeo says, and “the chance to serve your country.”
“We want to create an atmosphere where the likelihood of being of caught is high -- that is one of the ways to create an effective deterrent, but the reality is most cyber-crimes are resource intensive.”'
Shawn Henry, the former assistant director of the FBI’s cyber unit in Washington, says that even beyond the data challenge, cyber crime is difficult to solve because there are literally more suspects than any conventional crime. “In the late '80s and early '90s, when we responded to a bank robbery, the pool of suspects of those who may have robbed the bank was the number of people who were in the vicinity of the bank at the time it was robbed,” Henry says. “Today, when a bank is robbed electronically, the pool of suspects is limited to the number of people with a $500 laptop and an Internet connection.” He estimates that’s over a billion suspects.
Taddeo acknowledges that cyber units can face a higher rate of unsolved cases than divisions devoted to other crimes. “We want to create an atmosphere where the likelihood of being of caught is high -- that is one of the ways to create an effective deterrent,” Taddeo says, “but the reality is most cyber-crimes are resource intensive.”
Federal authorities also point to aggressive prosecutions of cyber espionage and financial crime, even in complex international circumstances.
Federal prosecutors in Pennsylvania indicted five Chinese military hackers for attacking energy and nuclear interests in the U.S. last year, a domestic case with major foreign policy implications. Last May, the FBI also helped lead coordinated arrests of over 100 suspects in 19 different countries, in connection with the abuse of a hacker technology, BlackShades. Many were prosecuted in their home countries, some were extradited, and the Justice Department secured six guilty pleas. Authorities hope those kind of cases provide an international deterrent for hackers who might assume they’re beyond the reach of American law.
“I think they thought they were safe behind the borders of jurisdictions that traditionally may not have cooperated with us,” says Taddeo, discussing hackers extradited to the U.S. in the BlackShades case.
What about ISIS?
Other foreign threats, of course, are well beyond conventional deterrence.
Many intelligence analysts study whether any terror groups, such as ISIS, could carry out a cyber attack on U.S. interests. The prevailing view is that while ISIS uses social media for messaging propaganda, it does not have the technical ability to pull off a sophisticated cyber attack.
Still, terror groups like ISIS might be able to outsource the job.
Mary Galligan, who led the FBI’s investigation into the September 11 attacks before handling a cyber portfolio, says that for ISIS, “It's a matter of can they get the tools -- and what would the target be.”
The dark web
She links that challenge to another growing problem in the cyber area, the sale of contraband, hacking services and violence to anonymous bidders online. “‘Hackers for hire’ is what we are talking about,” she says, where for sums as low as "a couple of thousand dollars," hackers may sell their services for a wide range of targets or plots. And while the notion of ISIS bidding on a U.S. cyber attack is largely hypothetical, the cyber black market for violence is not.
“You saw the FBI recently take down a case called 'Silk Road,'” Gaillgan recalls, “where you could go onto the ‘dark web’ where you could buy guns, drugs, and assassins for hire.”
The “dark web” is a hidden part of the Internet that most people never see. Since it isn’t accessed or “indexed” by most search engines, the average web user won’t stumble across its content. While there’s nothing automatically illicit about an underground repository of web pages, part of the dark web includes websites for virtual, anonymous criminal plotting.
New York’s top federal prosecutor, Preet Bharara, took the FBI’s case against the Silk Road portal to court, and won a conviction against a 30-year-old techie behind the operation, Ross Ulbricht. He now faces up to a life sentence. In a February interview with MSNBC, Bharara likened Silk Road to “an open-air bazaar on the Internet for the sale of all sorts of terrible things,” and he said authorities were vigilant in countering a new, virtual forum “for an old crime.”
In the end, there is nothing novel about the objectives of many cyber attackers, from theft to violence or even terror. Their methods, however, pose a legal and policy challenge that requires ongoing adaptation. Surveying that task for the FBI, special agent Taddeo concluded that complexity is part of the job. “There's no one easy solution -- there isn't the technology solution, there isn't a diplomatic solution to this problem,” he says. “It's a long-term issue that needs to be managed effectively at all levels of government, and at all levels of our private sector partners.”